
What is Deception Security (2026 Guide)
Learn how deception security works. How traps, lures, and decoys help detect attackers early and why it’s essential for modern SOC teams.

Learn how deception security works. How traps, lures, and decoys help detect attackers early and why it’s essential for modern SOC teams.
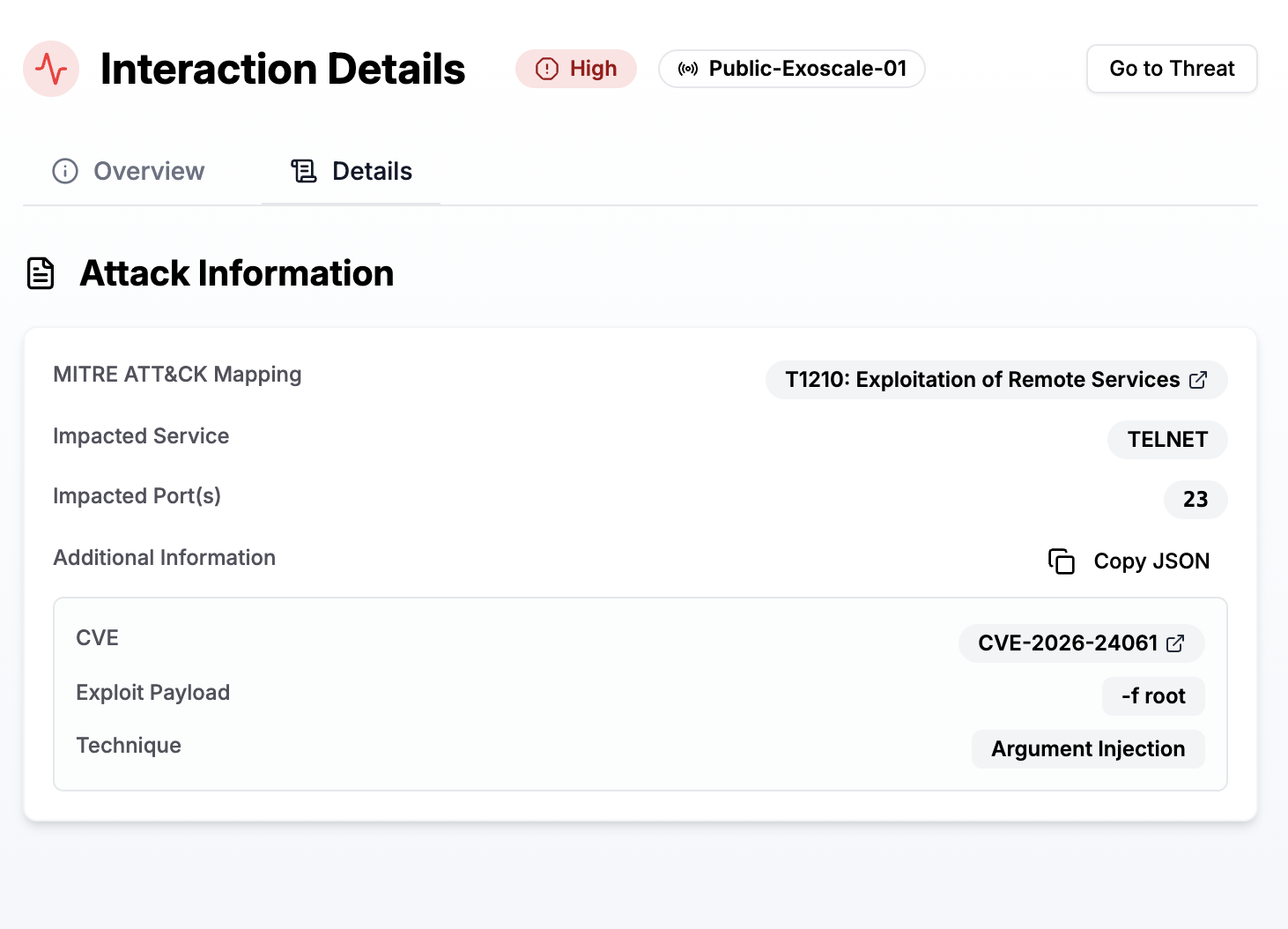
An 11-year-old vulnerability in GNU telnetd allows attackers to bypass authentication and gain immediate root shell access.

Discover the top honeypot and deception platforms in 2026, with open-source, for your SOC or security team.
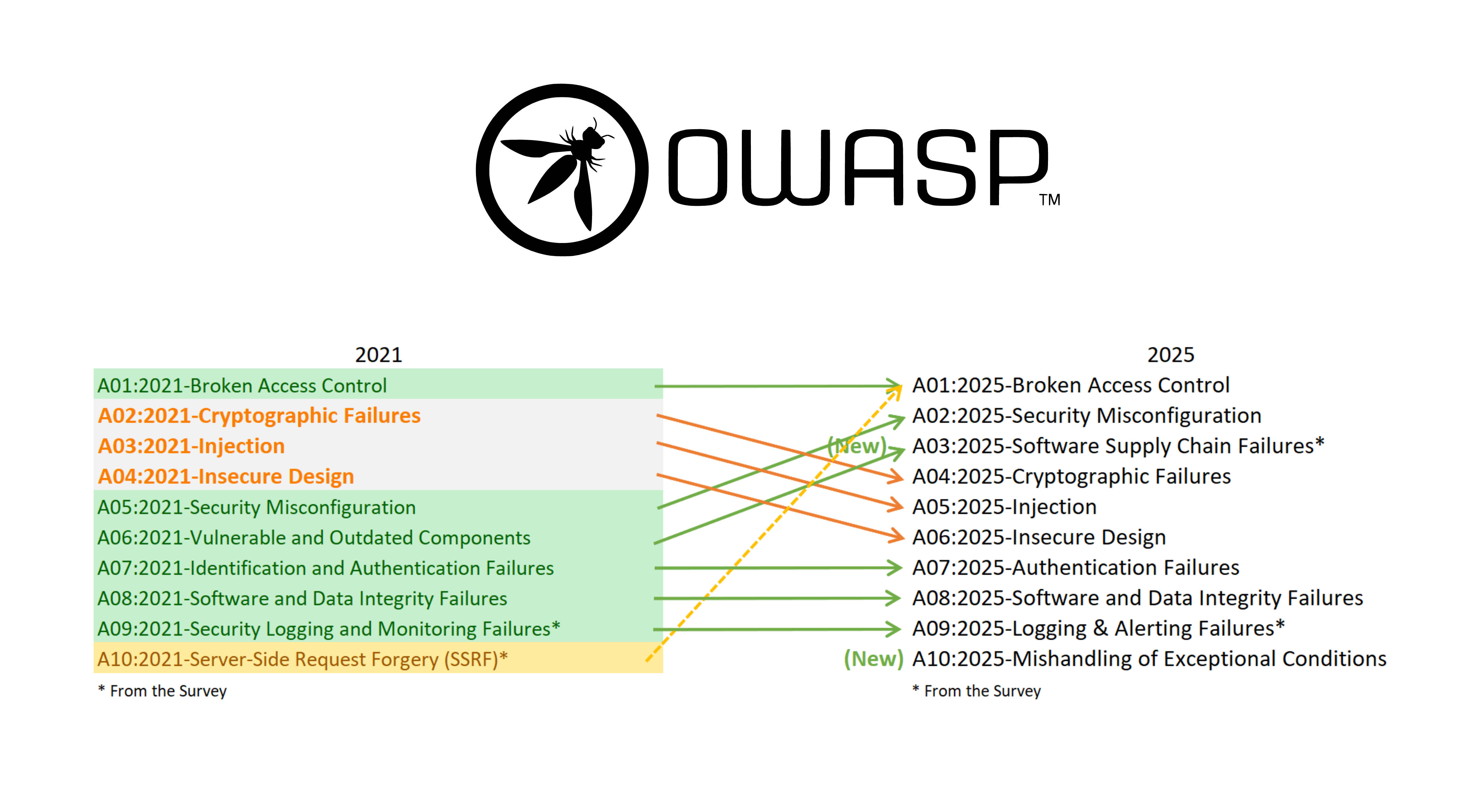
The OWASP Top 10 2025 is out, outlining the most critical security risks facing modern web applications. Two new categories have been added, but the central message remains unchanged: most breaches come from overlooked fundamentals.
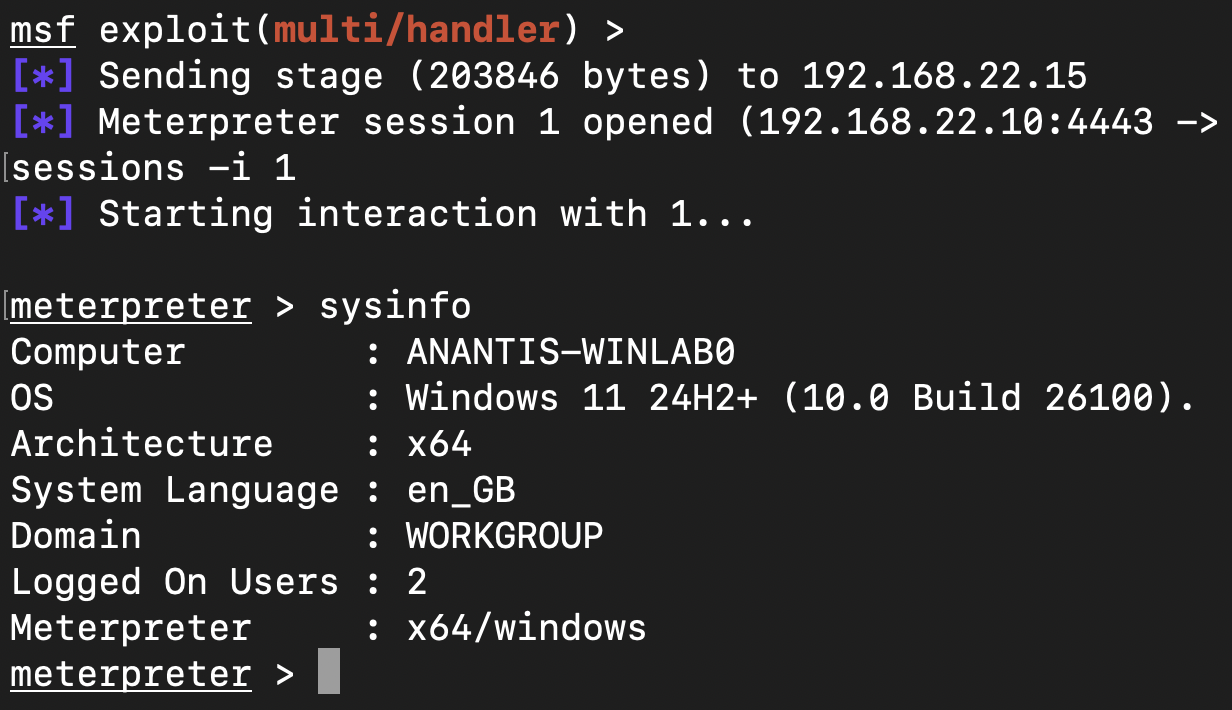
Researchers uncovered a Windows design flaw that lets attackers pause protected security processes via WerFaultSecure.exe, leaving organizations exposed until Microsoft releases a fix.
EDR - Endpoint Detection and Response - is a new type of antivirus far more powerful than traditional antivirus solutions.