· Théo Turletti · Anantis Security Labs · 2 min read
CVE-2026-24061: A Decade of Silent Root Access
An 11-year-old vulnerability in GNU telnetd allows attackers to bypass authentication and gain immediate root shell access.
What is CVE-2026-24061?
CVE-2026-24061 is a critical authentication bypass vulnerability impacting GNU InetUtils telnetd, a legacy remote access service still present on many embedded devices, network appliances, and OT environments. The issue arises from insecure processing of the USER environment variable transmitted via the Telnet protocol, which is passed directly to /usr/bin/login without any sanitization. Exploitation lets unauthenticated attackers inject arbitrary command-line flags, granting instant root shell access.
- Severity: Critical
- CVSS Score: 9.8
- EPSS Score: 29%
- Published: January 19, 2026
- Impact: Unauthenticated Remote Code Execution as Root
This flaw affects all systems running GNU InetUtils telnetd up to and including version 2.7-2. Although Telnet is a legacy protocol, global scans indicate over 1 million devices are still running Telnet servers. The vulnerability is actively exploited in the wild.
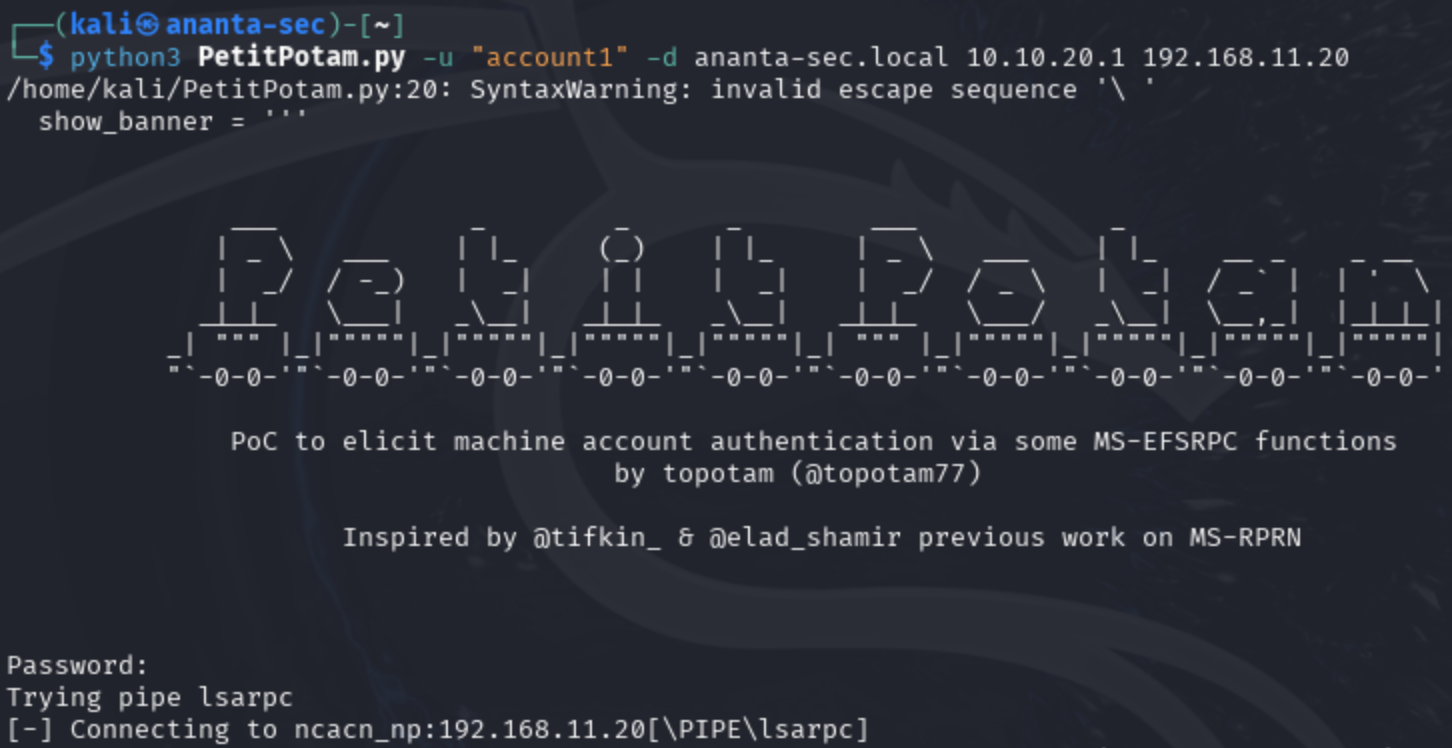
How the Vulnerability Works
GNU InetUtils telnetd delegates authentication to /usr/bin/login. The flaw lies in how the daemon handles the USER environment variable:
- Expected behavior:
telnetdpasses the username tologinfor verification. - Vulnerable path: The
USERvariable can be sent via the Telnet NEW-ENVIRON option.telnetdpreviously inserted this value directly into the login command without any sanitization. - Exploit: Setting
USER="-f root"results in the command:
/usr/bin/login -h <host> -f rootThe -f flag tells login to skip authentication entirely, granting an immediate root shell.
Impact: Full system compromise without credentials or user interaction.
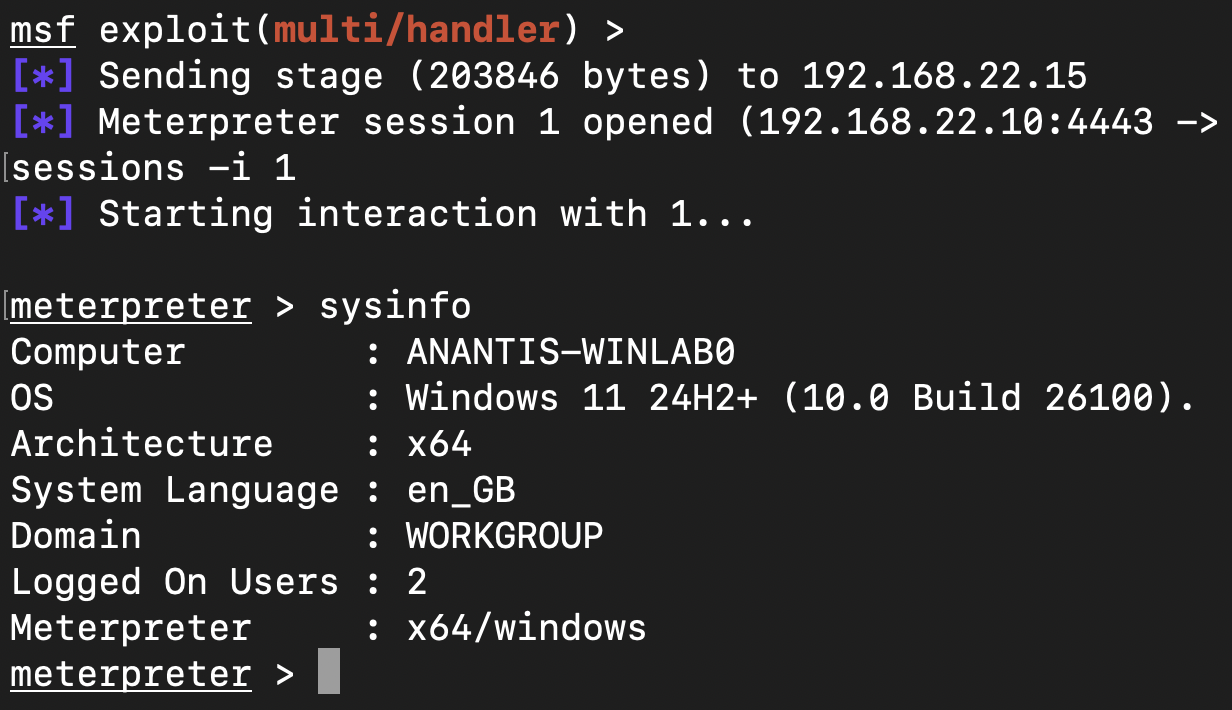
Exploitation Steps
- Attacker connects to a vulnerable Telnet service.
- Negotiates the NEW-ENVIRON option to set
USER="-f root". telnetdpasses this value to/usr/bin/login.- Root shell is immediately granted.
Proof-of-concept command:
USER='-f root' telnet -a <target_ip>Introducing Preemptive Detection with TrapEye
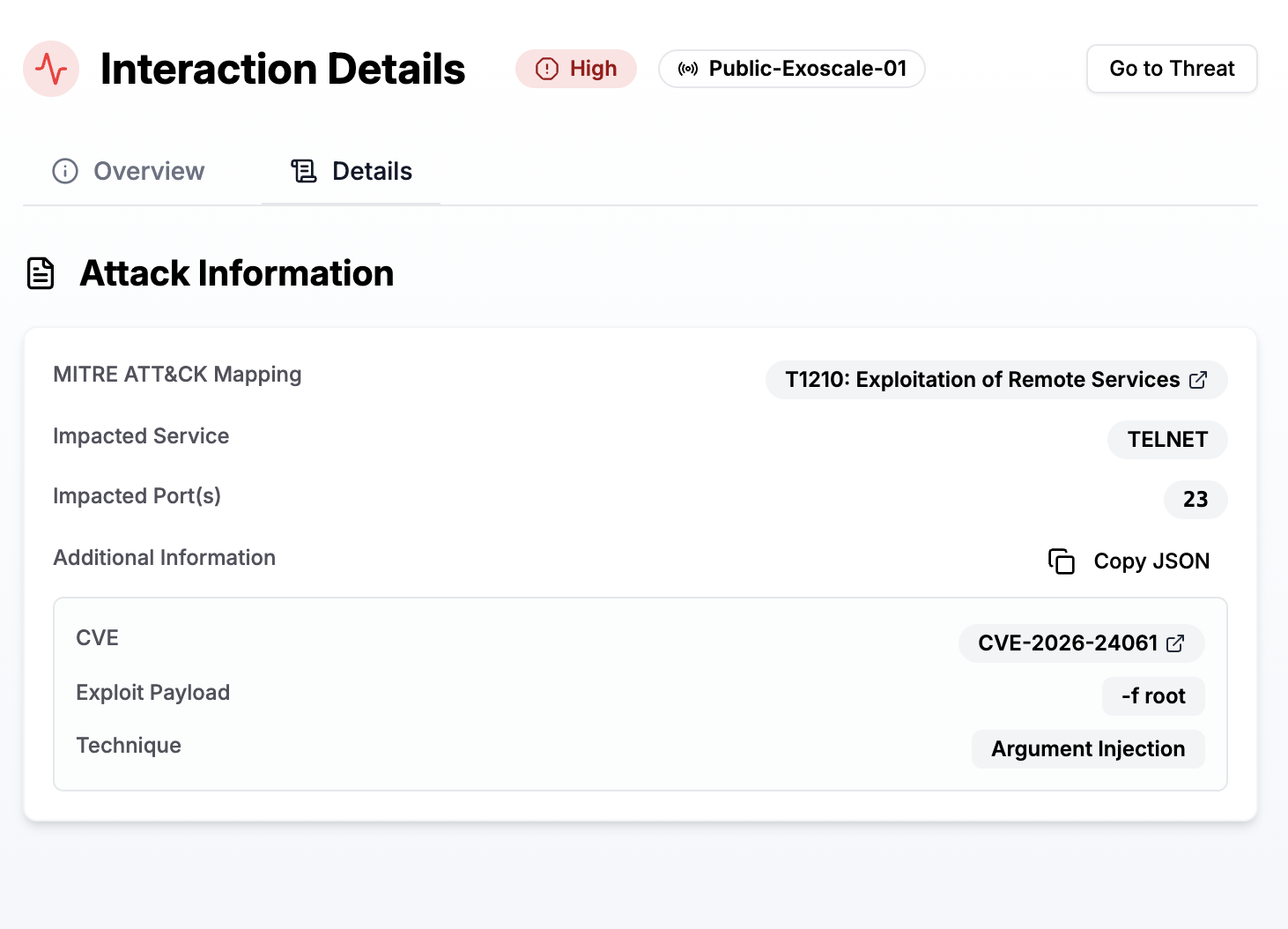
Although updated versions patch this flaw, many legacy systems remain exposed. Our platform automatically monitors for:
- Active exploitation attempts
- Malicious environment variable patterns
- Suspicious Telnet connection activity
TrapEye provides real-time alerts and attacker fingerprinting, enabling your team to isolate affected systems and stop attacks before damage occurs.
After several weeks of exposing a public trap, here is the aggregated Indicators of Compromise (IoCs) collected by Anantis.
| Attribute | Values |
|---|---|
| Unique IPs | 18 |
| Top Geolocation | The Netherlands |
| Top ASN | AS51396 Pfcloud UG |
Recommendations for Organizations
- Patch immediately to GNU InetUtils 2.7-2 or later.
- Disable Telnet wherever possible and use SSH for remote access.
- Segment legacy systems to reduce risk exposure.
- Deploy deception traps to detect exploitation in real time.
Conclusion
CVE-2026-24061 highlights the dangers of legacy protocols and the importance of proactive detection. A single oversight in handling the USER environment variable enabled unauthenticated root access for over a decade.
With TrapEye, your team gains immediate visibility into these exploitation attempts and can respond before damage occurs.