· Théo Turletti · For CISO · 2 min read
What is Deception Security (2026 Guide)
Learn how deception security works. How traps, lures, and decoys help detect attackers early and why it’s essential for modern SOC teams.

Definition of Deception Security
Deception Security is a cybersecurity approach that sets up decoy systems, traps, and fake assets to lure attackers and detect them as soon as they touch critical resources.
These interactions generate high-confidence alerts with near-zero false positives, allowing security teams to detect threats early in the attack lifecycle.
How Deception Security Works
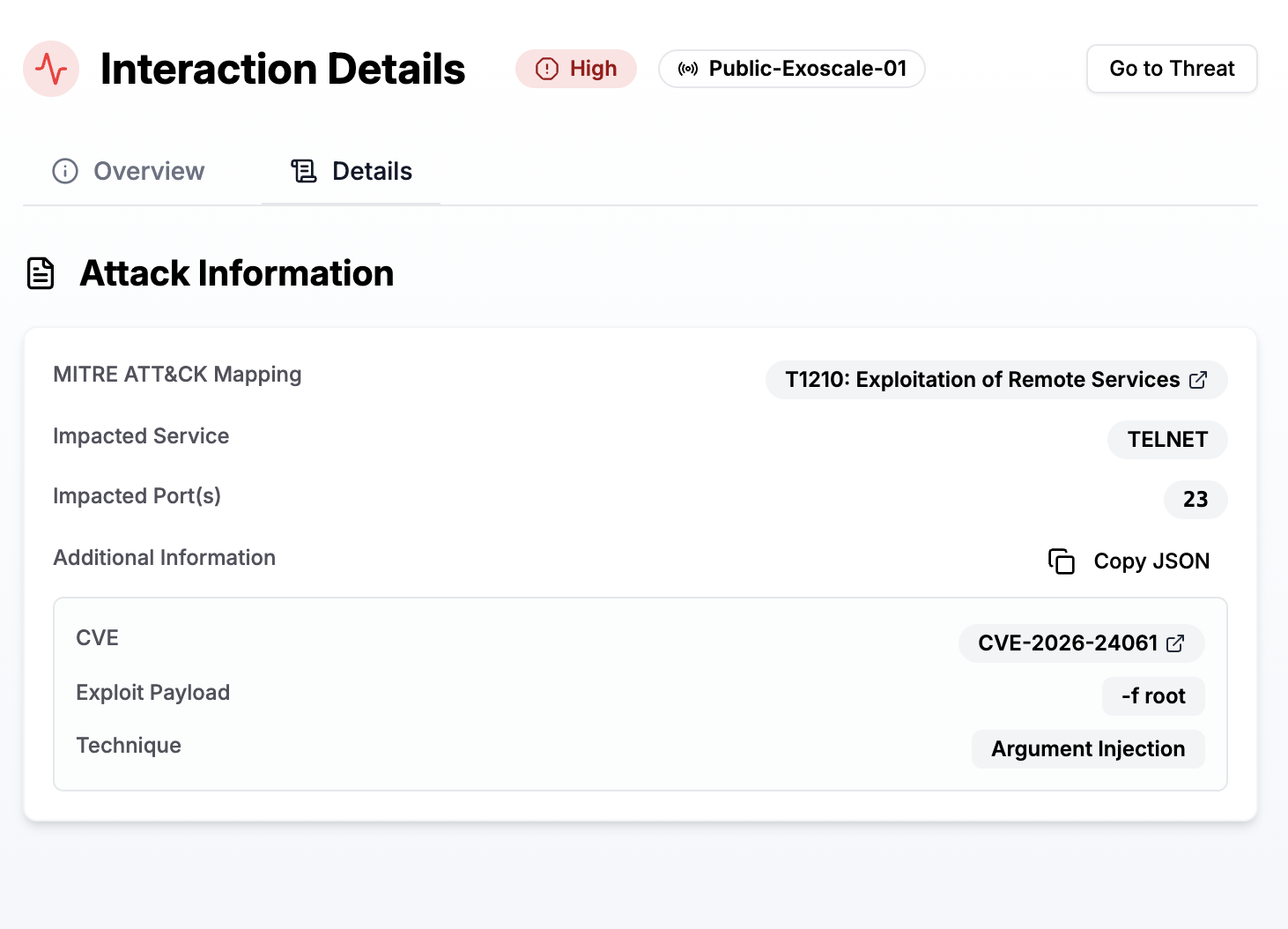
Deception security relies on three core components:
- Traps: Fake servers, endpoints, services that mimic real assets
- Lures: Fake credentials or files designed to attract attackers
- Detection Engines: Alerts triggered when an attacker interacts with these assets
Unlike traditional tools, detection is fully deterministic rather than probabilistic or AI-driven, resulting in low false positives.
Why Deception Security Matters in 2026
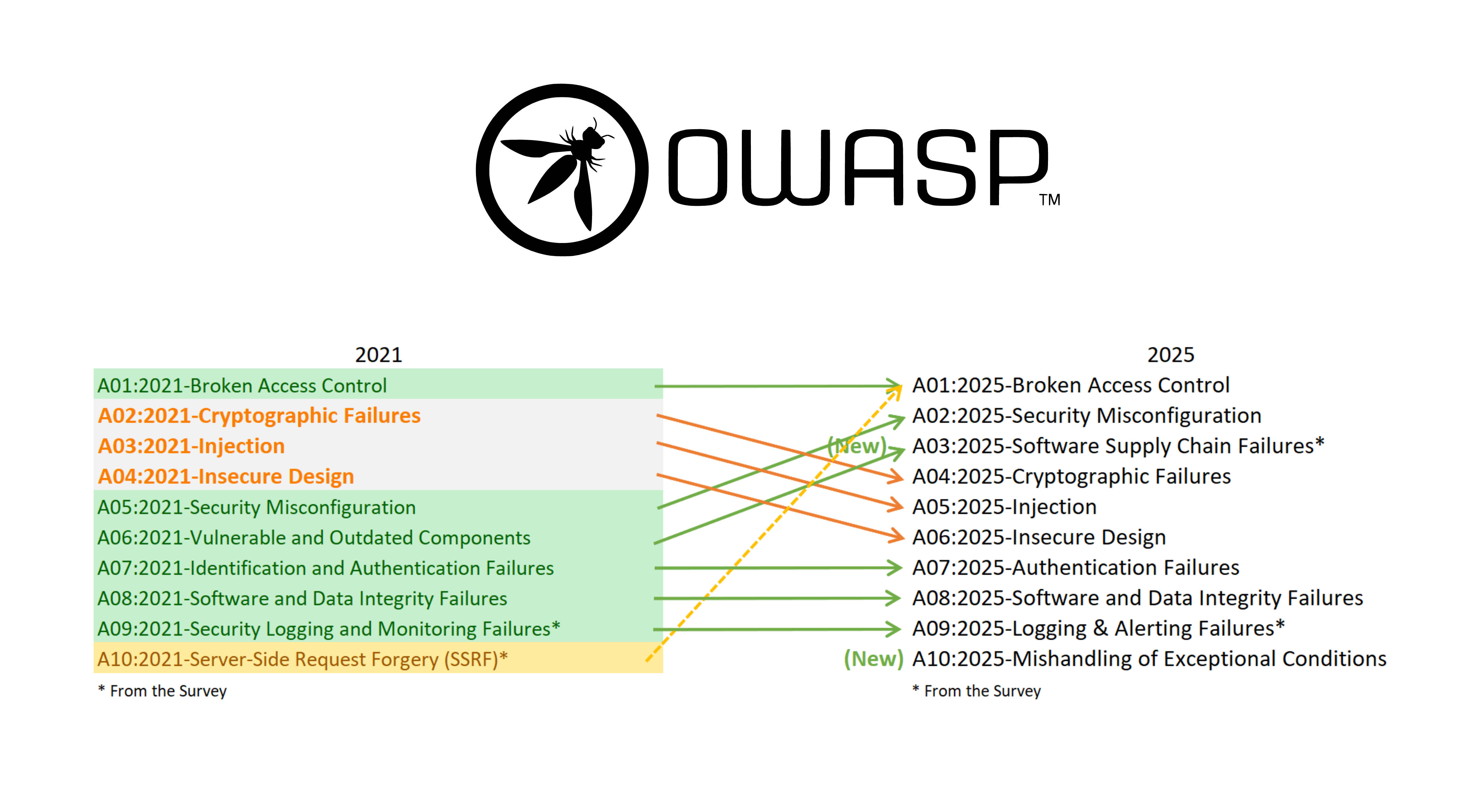
Modern attackers:
- Use legitimate tools (Living-off-the-Land)
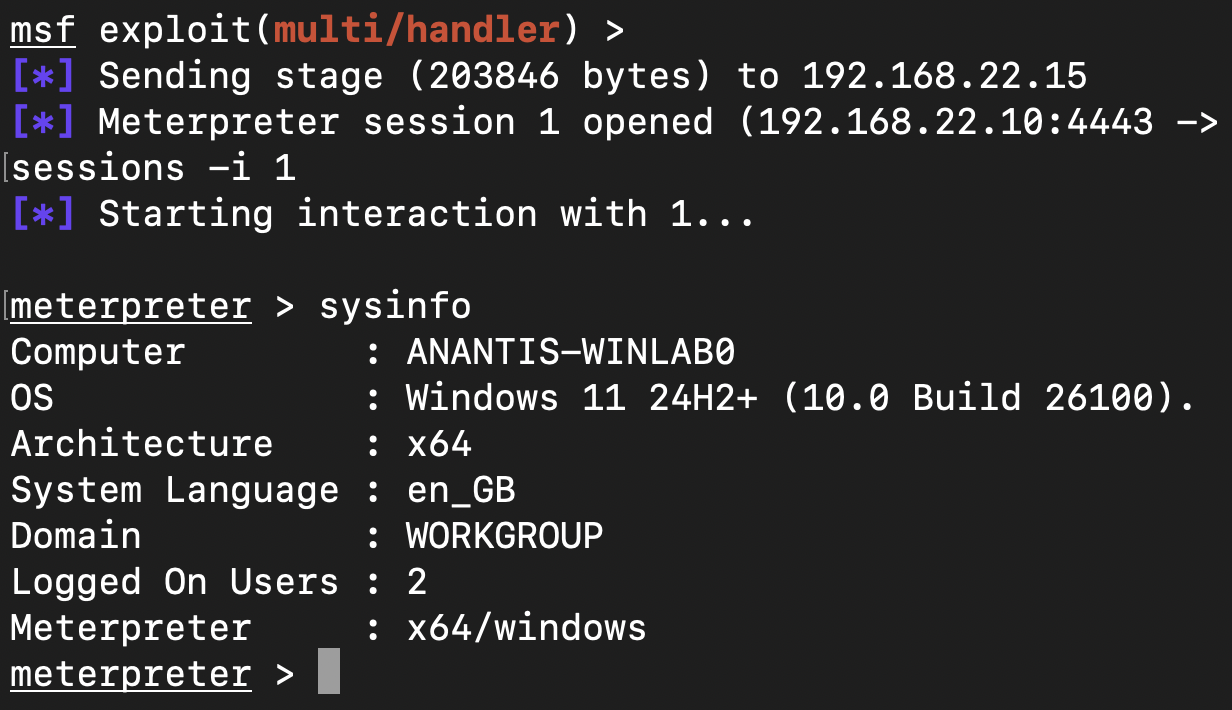
- Bypass EDR/XDR with advanced payloads
- Move laterally before triggering alerts
Deception security forces them to make a mistake.
Any interaction with a deception asset is a strong indicator of compromise.
Deception Security vs Honeypots
- Honeypots are isolated and often used for research
- Deception platforms are deployed across production environments and scale automatically
Deception security extends honeypots into a full detection strategy.
Key Benefits
- Near-zero false positives
- Early detection of attackers
- Visibility into lateral movement
- Works against unknown threats
Final Takeaway
Deception Security shifts your cybersecurity from reactive detection to proactive exposure of attackers.
Instead of running after threats, you take the lead and make attackers reveal themselves.
Learn more: https://anantis.io